Introduction
In today’s hyper-connected digital world, data breaches, ransomware attacks, and identity theft are no longer rare events, they’re daily headlines. From personal files and financial documents to business contracts and confidential communications, our digital assets are constantly at risk. The need for secure, private, and resilient data storage has never been greater.
This is where Anon Vault stands out. Built with advanced encryption methods and a powerful zero-knowledge architecture, it is designed to provide the highest level of digital security without compromising usability. Unlike traditional cloud storage platforms that may access or analyze your data, Anon Vault ensures that only you hold the keys to your information.
In this comprehensive guide, we’ll explore how Anon Vault works, what makes its security architecture superior, how it compares to competitors, and why it’s becoming a preferred choice for individuals and businesses seeking airtight privacy. Whether you’re a privacy advocate, business owner, or everyday user, this article will help you understand how to ensure top-tier protection in a rapidly evolving cyber threat landscape.
What Is Anon Vault and Why Digital Security Matters
Anon Vault is a secure digital storage platform built around end-to-end encryption and a zero-knowledge framework. Its primary goal is to protect user data from unauthorized access including from the service provider itself.
As cybercrime continues to grow (global cybercrime costs are projected to exceed $10 trillion annually according to Cybersecurity Ventures), secure digital storage is no longer optional. It’s essential.
Why Digital Security Is Critical Today
- Increasing ransomware and phishing attacks
- Cloud storage vulnerabilities
- Insider threats within organizations
- Government and third-party data surveillance
- Data privacy regulations (GDPR, CCPA compliance needs)
What Makes Anon Vault Different
- Client-side encryption before data leaves your device
- Zero-knowledge infrastructure
- Multi-layered security architecture
- Secure authentication mechanisms
- No data mining or tracking
It is positioned within the privacy-first technology niche, serving individuals, enterprises, journalists, developers, and anyone who values confidentiality.
By combining usability with military-grade encryption, it addresses one of the greatest challenges in cybersecurity: protecting data without making access overly complex.
Understanding Advanced Encryption in Anon Vault
At the core of Anon Vault lies its advanced encryption methodology. Encryption converts readable data into unreadable ciphertext that can only be unlocked with a secure key.
Key Encryption Technologies
- AES-256 encryption (Advanced Encryption Standard)
- RSA-4096 key exchange
- End-to-end encryption protocols
- Secure hashing algorithms (SHA-3)
- Perfect Forward Secrecy mechanisms
How It Works
- Data is encrypted locally on your device.
- Encryption keys are generated securely.
- Only encrypted data is transmitted to servers.
- Without your key, decryption is mathematically infeasible.
Why AES-256 Matters
AES-256 is widely recognized as one of the strongest encryption standards. It is:
- Used by government agencies
- Resistant to brute-force attacks
Even with massive computing power, decrypting AES-256 without the key would take billions of years.
Zero-Knowledge Architecture: What It Means for You
Zero-knowledge architecture is one of the most powerful features of Anon Vault. It means your data is encrypted directly on your device before it is uploaded, and only you hold the encryption keys. Not even Anon Vault can access, read, or decrypt your files. This ensures complete privacy and removes the need to rely solely on the provider’s internal security policies.
Unlike traditional cloud storage systems that use server-side encryption, it exposed to the server, and all stored files remain fully encrypted. Even in the event of a server breach, attackers would only encounter unreadable encrypted data without the private keys required to unlock it.
This zero-knowledge framework protects users from insider threats, data mining, surveillance, and unauthorized third-party access. It represents one of the strongest privacy models available in modern cybersecurity. By eliminating access at the structural level, it ensures that control over your digital information remains entirely in your hands.
Multi-Layered Security Mechanisms

Security isn’t just about encryption. It integrates multiple defense layers to create a resilient ecosystem.
Core Security Layers
- Two-Factor Authentication (2FA)
- Biometric access (where supported)
- Device authentication controls
- Session timeout management
- IP anomaly detection
Additional Protective Measures
- Secure key derivation functions
- Brute-force attack prevention
- Rate limiting and monitoring
- Encrypted metadata protection
Defense-in-Depth Strategy
Anon Vault applies a defense-in-depth approach, meaning if one layer fails, others remain intact.
For example:
- Even if login credentials are compromised, 2FA blocks access.
- Even if servers are breached, encrypted files remain unreadable.
- Even if a session is hijacked, auto-logout prevents data exposure.
This multi-layered design makes Anon Vault resilient against:
- Phishing attacks
- Credential stuffing
- Malware threats
- Network interception
Security experts often emphasize that no single security feature is enough, layered protection is key. Anon Vault follows this industry best practice closely.
Anon Vault vs Competitors: A Detailed Comparison
Choosing secure storage requires comparing options carefully. Below is a simplified comparison:
| Feature | Anon Vault | Standard Cloud Storage | Encrypted Cloud (Basic) |
| Zero-knowledge | ✅ | ❌ | Sometimes |
| Client-side encryption | ✅ | ❌ | ✅ |
| AES-256 | ✅ | ✅ | ✅ |
| Metadata encryption | ✅ | ❌ | Limited |
| Data mining | ❌ | Often | Rare |
| Advanced authentication | ✅ | Basic | Moderate |
Key Differentiators
- Full zero-knowledge implementation
- No data tracking or analytics
- Strong metadata protection
- Enterprise-ready architecture
While many providers claim encryption, not all implement true zero-knowledge systems. Anon goes further by integrating encryption into its core infrastructure rather than treating it as an add-on.
Real-World Case Study: Business Data Protection
A mid-sized legal firm managing confidential contracts and sensitive client data faced growing concerns about privacy and regulatory compliance while using traditional cloud storage. Although their previous provider offered encryption, it relied on server-side controls, which meant there was still potential exposure risk. With increasing cyber threats and strict data protection regulations, the firm needed a more secure and private solution.
After switching to Vault, all files were encrypted locally before being uploaded to the cloud. The firm implemented two-factor authentication across all accounts and restricted internal access permissions. Because of Anon Vault’s zero-knowledge architecture, even the service provider could not access client documents, significantly reducing the risk of insider threats or external breaches.
Within months, the firm strengthened regulatory compliance, improved client trust, and reduced overall cybersecurity risk. This case highlights how Anon Vault is not just a storage platform but a strategic security investment. For businesses handling sensitive information, advanced encryption and zero-knowledge protection provide long-term protection and peace of mind.
Privacy, Compliance, and Legal Protection
Data privacy laws are becoming stricter worldwide. Organizations must comply with:
- GDPR (Europe)
- CCPA (California)
- HIPAA (Healthcare)
- SOC 2 standards
Anon Vault supports compliance through:
- Secure encryption protocols
- Data minimization practices
- User-controlled access
- Audit-friendly architecture
Zero-knowledge systems also protect companies legally because providers cannot disclose data they cannot access.
This reduces:
- Legal exposure
- Third-party liability
- Compliance risks
Privacy-focused infrastructure aligns with global regulatory trends.
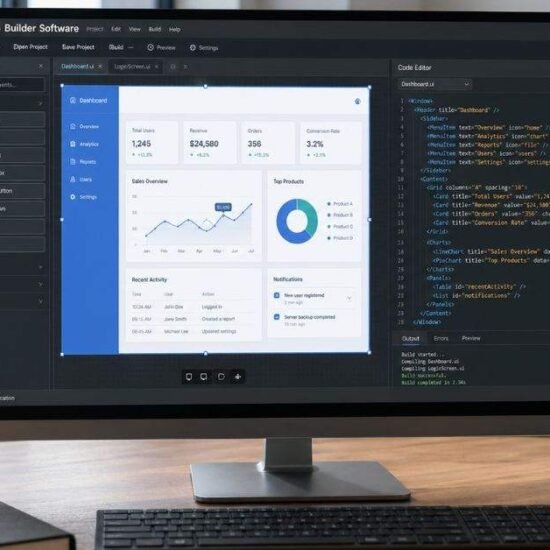
User Experience Without Compromising Security
High security often means complicated interfaces but Anon Vault balances both.
Key UX Features
- Intuitive dashboard
- Secure file sharing
- Encrypted collaboration tools
- Cross-device compatibility
- Automated secure backups
Seamless Security Integration
Users don’t need advanced technical knowledge to benefit from the following:
- Automatic encryption
- Secure key generation
- Easy 2FA setup
By combining usability with enterprise-grade encryption, it removes friction while maintaining strong protection.
Best Practices for Maximizing Anon Vault Security
Although Anon Vault provides advanced encryption and zero-knowledge protection by default, users can enhance security further by following smart practices. Creating a strong, unique master password and enabling two-factor authentication are essential first steps. Since zero-knowledge systems limit password recovery options, securely storing backup keys is critical.
Keeping devices updated, avoiding unsecured public Wi-Fi, and monitoring account activity also reduce risks. For even stronger protection, users can integrate hardware security keys or biometric authentication. By combining Anon Vault’s resilient security architecture with responsible user habits, you achieve maximum digital protection.
The Future of Digital Security with Anon Vault
As cyber threats evolve, encryption technologies must adapt. The future includes:
- Quantum-resistant encryption
- AI-powered threat detection
- Decentralized storage models
- Enhanced biometric security
Anon Vault’s architecture is designed to evolve with:
- Modular encryption upgrades
- Continuous security audits
- Adaptation to new regulatory frameworks
The shift toward zero-knowledge systems is accelerating. Privacy-first technology is no longer niche, it’s becoming mainstream. It positions itself at the forefront of this digital security revolution.
FAQs
What makes Anon Vault more secure than traditional cloud storage?
Anon Vault uses client-side encryption and zero-knowledge architecture, ensuring even the provider cannot access your data.
Can Anon Vault employees access my files?
No. Zero-knowledge encryption prevents employees and third parties from decrypting data.
Is Anon Vault suitable for businesses?
Yes. Its encryption, compliance support, and multi-layered security make it ideal for enterprises.
What happens if I forget my password?
Because of zero-knowledge encryption, recovery options are limited. Securely storing recovery keys is essential.
Does Anon Vault comply with privacy regulations?
Its architecture supports GDPR and other data protection standards, helping organizations maintain compliance.
Conclusion
In an era defined by data breaches and digital surveillance, protecting your information requires more than basic encryption. Anon Vault outperforms others with its advanced encryption methods and zero-knowledge architecture, ensuring that only you control access to your digital assets.
From AES-256 encryption and multi-layered security mechanisms to compliance support and seamless user experience, it delivers enterprise-grade protection for individuals and businesses alike. Its defense-in-depth strategy, privacy-first design, and resilience against evolving cyber threats make it a powerful solution in the digital security landscape.
If safeguarding sensitive information matters to you whether personal files or business-critical data, exploring could be a transformative step toward uncompromised digital privacy. The future belongs to zero-knowledge security, and it is leading that charge.